 | |||
|
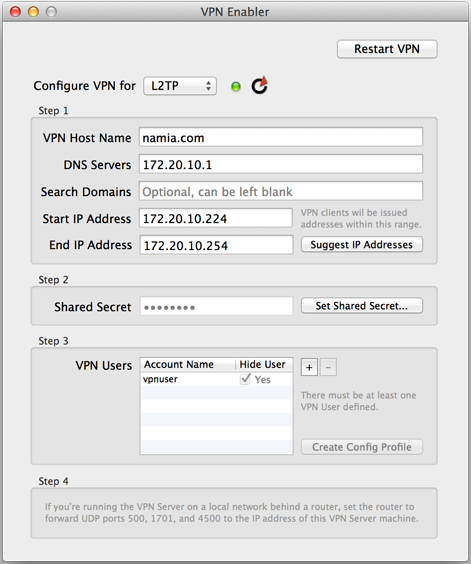
VPN Enabler for El Capitan There is a VPN Server built into every plain Mac OS X machine, only it's not activated unless you know how to type in a lot of geeky commands and dive into a lot of configuration files. What VPN Enabler does is to do all that stuff for you in just three (OK, maybe four) steps and just one click. VPN Enabler now supports both L2TP and PPTP protocols. Setting up the VPN Server This is what VPN Enabler looks like. Step 1. You only need to provide the Host Name for your VPN Server. Of course, this host name or domain name must be accessible from the Internet. Then, look for the “Suggest IP Addresses” button. If you’re running VPN Enabler on the single machine on the local network, behind the router, that has all the Internet services loaded on it (e.g., web, mail & DNS server, all on one machine), which is quite a reasonable assumption for the user base that is running all my “enabler” apps, then when you click on that “Suggest IP Addresses” button, it’ll try to provide you with reasonable values that you can use. These values are provided to an incoming VPN client, on joining the local private network. It'll be assigned an IP address within the range you provided, and then it’s told where to go for DNS services. Basically, the VPN Server acts like a DHCP Server for incoming VPN clients.
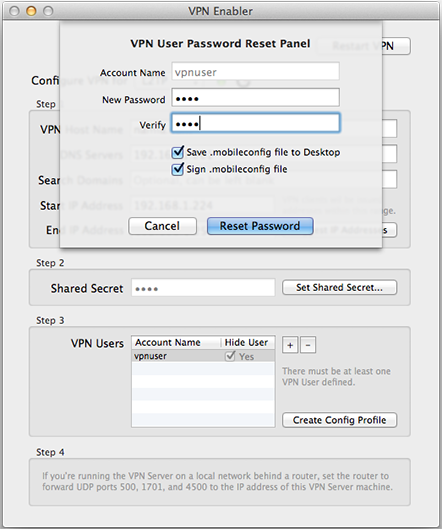
Step 2. Enter a Shared Secret, which is just a word you need to enter into a VPN client, like Network Preferences on a client Mac or the VPN Connection Setup in iOS Preferences for the iPhone or iPad. Step 3. Set up at least one VPN user account on your server machine. Give it a name and a password. Both will also be given to the VPN Client. (Use a name that has not been used and especially not the name of an admin user. The VPN User will be created as a simple non-admin user because you don’t want to be logging on to your VPN as an admin-level person from wherever you are in the world). Step 4. An Important Tech Note : NOTE : I’ve just set up a VPN Server behind a router that didn’t require me to do all the following port forwarding things. So you may get lucky and there’s no Step 4. Usually this is a router that allows you to set a DMZ, an internal IP address that all traffic from external IP addresses get directed to, for internet services. Try this first. If it works, you can stop here for the VPN server. You don’t have to set up port forwarding for VPN ports manually. If you’re not so lucky, this is a bit more technical. If you’re running the VPN Server on a local network behind a router, you need to figure out how to set up the router to forward UDP ports 500, 1701 and 4500 to the local IP address of your VPN Server machine (and also port 1723 if you want to support PPTP). This is not as difficult as it sounds. Your router (which might be bundled with a wifi base station) would have a setup page that you can access using a web browser. Look for the Port Forwarding setup page, which is probably lumped with the Firewall settings. Then use that setup page to create three port forwarding records to associate UDP ports 500, 1701, and 4500 with the local IP address of the Mac that is running your VPN Server. This way, when network traffic comes in from a VPN client, the router will know which machine to route them to for processing. Setting up the VPN Clients 1. The Automated Way From version 1.0.3 onwards, VPN Enabler allows you to save a mobileconfig profile that can be sent (e.g., by email) to the user of both an iOS device or the Mac, and it’ll save the user from having to know all of the following configuration steps for a VPN client. All the user has to do is to tap on the .mobileconfig file that he sees (if he’s on iOS) or to double-click on it (if he’s on a Mac), and follow through with the automated installation steps. He’ll have everything set up for him and all he has to do is to make the VPN connection (in the Settings app, on iOS) or via Network Preferences (on the Mac). VPN Enabler gives the administrator two ways to generate a .mobileconfig file. One way generates a profile without the VPN user password, and this is available from the main VPN Enabler window. The other way is more convenient, because it includes the password, allowing the user to just focus on making the VPN connection. This other way is available when the user is either creating a new VPN user account or resetting the user account password, and it’s shown below :
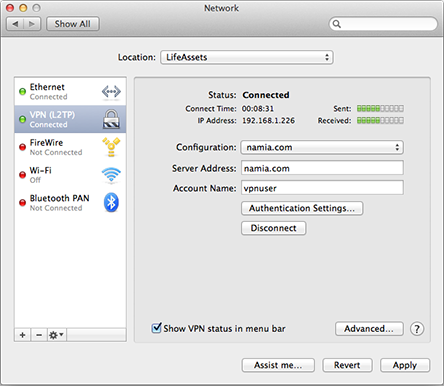
On top of saving the profile, the administrator is also encouraged to sign the profile, if the server VPN Enabler is running on has the SSL cert for the domain installed (in OS X’s OpenSSL folder in /System/Library). 2. Manually Setting up VPN Clients On the Mac client, set up your VPN configuration like this in Network Preferences, by entering the VPN Server’s host name and the VPN user account name :
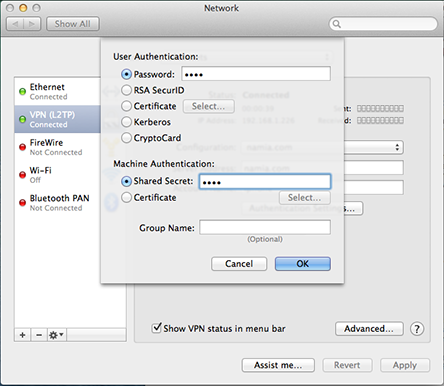
Click the "Authentication Settings" button and enter the VPN User account password and the Shared Secret :
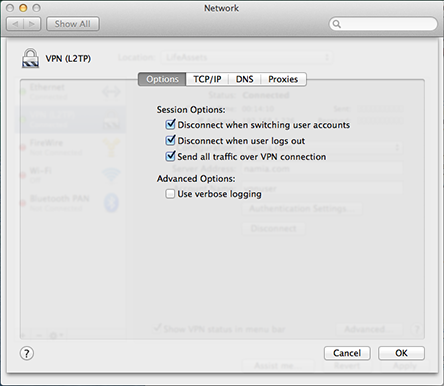
And click the Advanced… button to set the “Send all traffic over VPN connection” option:
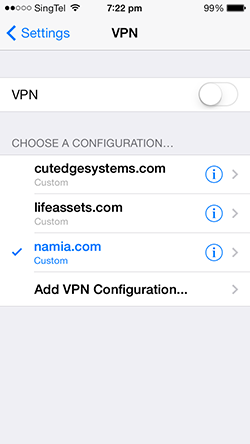
For iOS clients, look for Settings > General > VPN. Add a VPN Configuration:
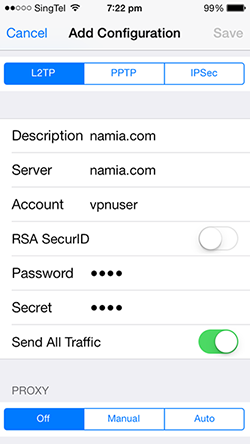
and, in the Add Configuration panel, do this:
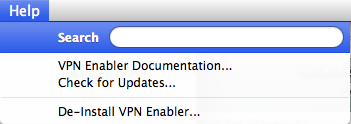
And that’s all there is to it. Enjoy! De-Installing VPN Enabler You can de-install VPN Enabler by using the last menu item in the Help menu. It will shut down the VPN Server, if it is running, and remove all files installed by VPN Enabler (in /usr/local/cutedge/vpn).
3.0 October 6th 2015. VPN Enabler for El Capitan released. I coundn’t get the VPN Server to authenticate the client using MSCHAP2 on El Capitan. So, in order to have something usable on El Capitan again, I downgrade the authentication protocol to PAP, whereby passwords are sent in the clear. Obviously not so good. 3.0.1 October 8th 2015. I’ve got authentication using MSCHAP2 working again, so the authentication process cannot be snooped. Download this version and do a De-Install from the Help menu to get things working again the way it should. 3.0.2 October 10th 2015. VPN Enabler now supports PPTP, for those needing to support devices that don’t work well with L2TP. Thanks, Gordon Aspin, for sharing :) Currently, VPN Enabler allows you to set one or the other protocol, but not both at the same time. Also, you can now generate mobile config profiles for PPTP (but of course). I love this one-click way of setting devices. Must import the technique into my other “enabler” apps. This version also brings back the ability to sign the mobileconfig profiles, if you have either a real cert or a test cert in /usr/local/cutedge/ssl (as you would have if you’re using the other “enabler” apps, like MailServe or WebMon). 3.0.3 October 13th 2015. Some minor bug fixes. Added info about forwarding port 1723 for PPTP. If you’re lucky with the router, you can skip this step entirely. 3.0.4 October 15th 2015. Fixed a bug with the de-install process, whereby the login dialog box makes a strange re-appearance. 3.0.5 July 18th 2016. Minor bug fixes. 3.0.6 August 12th 2016. VPN Enabler had a bug whereby if a user, when asked to choose a name for the VPN User, enters the name of the admin user he is currently using to log on to his Mac (he is supposed to enter a name that has not been used at all and it will be created as a non-admin account, because you don’t want to log on to your VPN as an admin user, from any device, anywhere in the world). I had actually checked for this, and in most cases the check will work (i.e., VPN Enabler won’t allow you to use an existing account as the VPN User). But there is one case where the check will fail – when the user enters an admin account name that has capitals in it. I had assumed that all OS X user short names are in small letters, no caps – because that’s the way the system will set it by default when it creates a short name from a user long name. But I hadn’t known that you could go back and force-capitalise some and any of the letters. So when I check my lower-case VPN user name against the list of existing names, and I’m doing a case-sensitve Unix grep by default, it will fail to spot that a mixed-case variant already exists among the user names. The worst case is that this is the admin user, himself. VPN Enabler will then clobber his admin user’s account settings (with the settings intended for the standard, non-admin VPN user), hiding the admin user account from the login screen and changing his userID, and thus render the admin account inaccessible, unusable and locked out of his Mac. An altogether terrible situation. I’m really sorry for this bug, all those who’ve suffered from it. I’ve now fixed this in version 3.0.6, by simply doing a case-insensitive check against the existing user names, so as to find a mixed-case variant of the one that the user has chosen as the VPN User, and so protect the existing user account from damage. Thanks to Jeremy Lewis for patiently taking me through all the steps he had taken, so I can reproduce the bug. |
Download The latest version of VPN Enabler is 3.0.6 Please check out the Release Log
There is a VPN Enabler for Mojave |
||